Platform
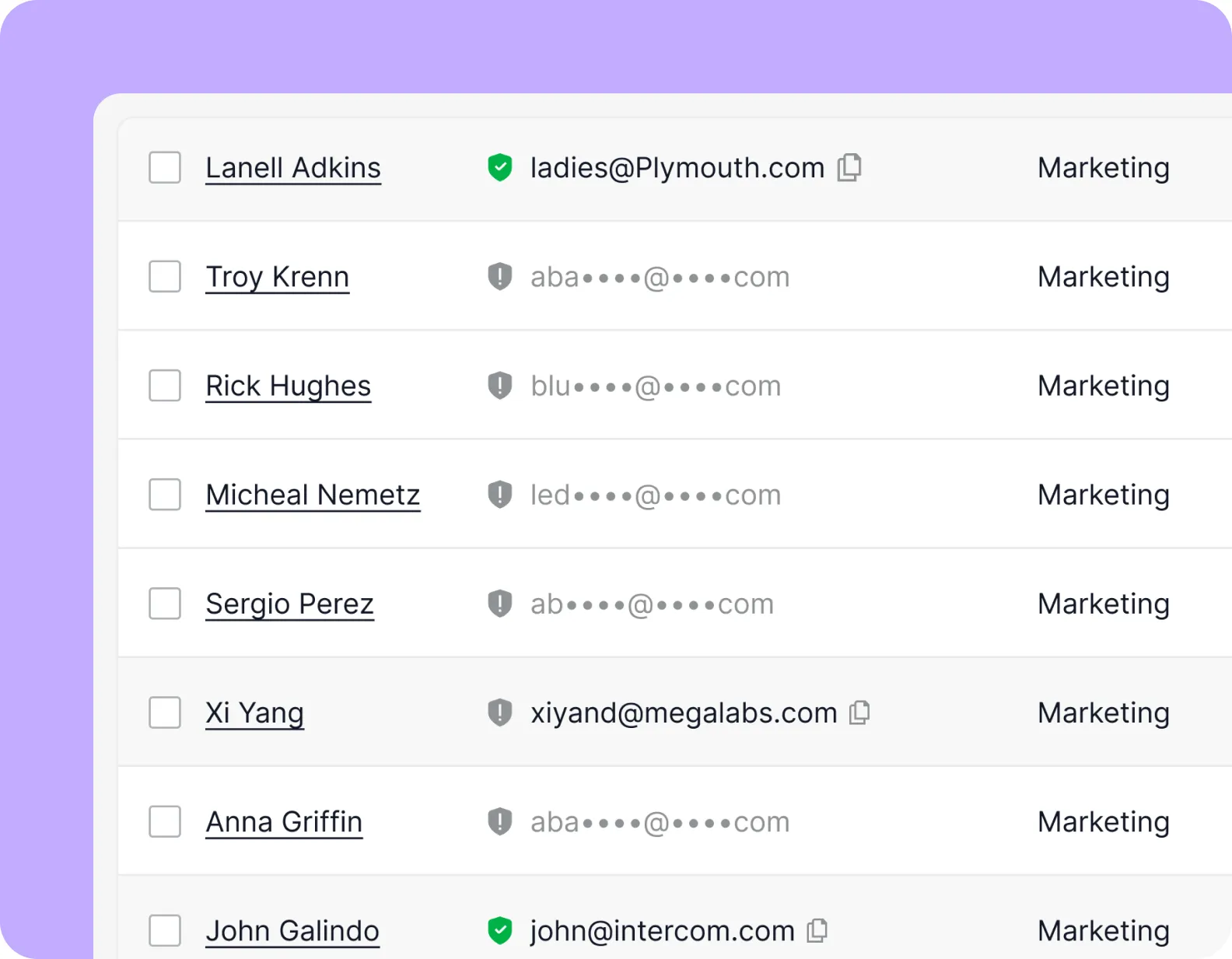
- ProspectorReach new prospects with 97% accuracy in seconds
- Data EnrichmentAppend your contact/company lists with 100+ data points
- Chrome ExtensionGrab leads straight from LinkedIn and company websites
- Job PostsFind all prospects who are actively Hiring For
- TechnographicsFilter 60K+ web technology data points
Email Lists
B2B Email Lists
Resources
CASE STUDIES
Learn why 20,000+ industry leaders using Bookyourdata.
Others
Diverse industries, unified by success with Bookyourdata.